Strengthen Your Password Protocol for Maximum Security


In today's world, cybersecurity is more important than ever, and one of the most crucial aspects of online security is the strength of our passwords. According to a recent study, it is estimated that 81% of company data breaches are caused by the use of poor passwords. Let’s talk about the best practices for strengthening your company’s password protocol to improve security and prevent data breaches.
How Strong is Your Password?
The true strength of a password is how well it will perform against password-cracking software. No password is 100% safe, but certain passwords can be exponentially more difficult to crack than others. Password entropy is a measure of how strong a password is. It is a mathematical formula that calculates the unpredictability of a password, which is critical to maintaining online security.
A strong password is one that is complex and difficult to guess, with a high level of entropy. Password entropy takes into account the number of characters in a password, the type of characters used, and the randomness of those characters. For example, a password consisting of a mix of uppercase and lowercase letters, numbers, and symbols such as SnailGiantBroomWhite$#!1645 is much stronger than a password made up of just letters. In the end, the strength of your password ultimately comes down to its entropy.
Creating a Long & Unique Password
Follow these tips and you’ll have a strong password in no time. Use a combination of uppercase letters, lowercase letters, numbers, and special characters and symbols. Make the password at least 12 characters long. Longer is stronger! Use a different password for each account or application. Consider a passphrase of random unique words.
Creating a strong password, or passphrase, also includes avoiding patterns like dates and sequential numbers or keyboard letters (qwerty). Avoid reusing old passwords, even if you have changed them slightly. And even though it seems helpful, don’t use common substitutions, such as replacing "o" with "0" or "s" with "$” because these are still easy to hack. Never write down your password, and make sure to enable lockout policies that lock your account after a number of unsuccessful login attempts.
Understanding Password Attacks
Brute-force password hacking is a technique cyber criminals use to guess a user's password by systematically trying every possible combination of characters until the correct one is found. It’s a time-consuming and sometimes expensive method, but it can be effective if a password is weak or simple. The process involves using automated software or tools to generate a list of potential passwords, typically starting with the most common ones and then systematically trying each until the correct password is found. Brute-force attacks can take anywhere from a few hours to several years to crack a password, depending on the length and complexity of the password.
Another type of cyber attack is called a dictionary attack. This is a technique that attempts to guess a password or encryption key by using a list of words found in a dictionary or commonly used words, phrases, or passwords. In this type of attack, the attacker uses a program that systematically tries different words and word combinations from a list in an attempt to find the correct password or encryption key. To protect against dictionary attacks, using strong passwords that are not easily guessable is important. Combining random, unique words can help add layers of protection.
Staying Secure with 2FA or MFA
Two-factor authentication (2FA) offers a higher security level than just a password or passcode. An authentication method using two factors usually involves a password as the first factor and a security code or biometric factor, such as a fingerprint or facial scan, as the second. The two-factor authentication process is more secure because, even if a victim's password is hacked, a password alone is not enough to pass the authentication check, making it harder for attackers to gain access to their devices or online accounts.
An authentication method that uses more than two verification factors is known as multi-factor authentication (MFA). Usernames and passwords are vulnerable to brute-force attacks and can be stolen by cybercriminals. Using an MFA factor like adding a thumbprint and security code along with a password increases your level of security. Did you know that 99.9% of password hacking attempts are blocked by using at least two-factor authorization?
Benefits of Using a Password Manager
Another way to keep your data secure is with a password manager, which stores multiple passwords in a single account. This is beneficial because most people have as many as 100 accounts, making it nearly impossible to remember every password. Password managers can create strong, random passwords for each of your accounts. This can help guarantee a high level of entropy for all of your passwords. With password managers, you can easily change your passwords. This benefit allows you to change more than one password at a time, while only having to remember the login to the password manager itself.
If you have joint accounts with someone, password managers allow you to share passwords from one user to another in a secure fashion. This allows users to protect passwords by not having to share them via text, email, or another insecure method. Password managers can be used across multiple devices, which allows for a seamless password management experience, regardless of which of your devices you are using. They have proven to be an effective way to create and keep strong passwords as a user's digital footprint grows over time.
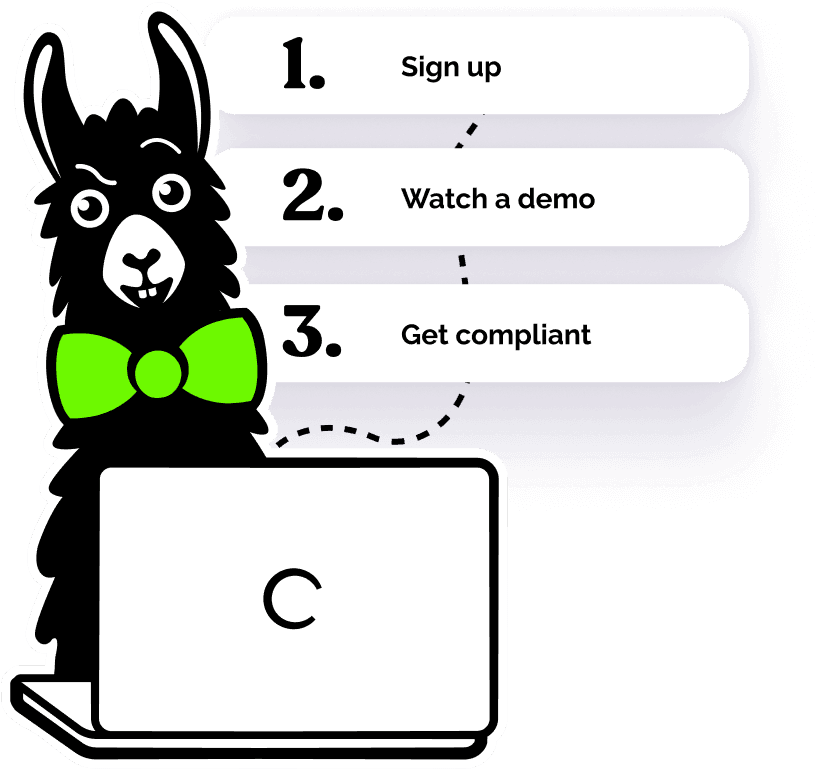
What’s Next?
Does your workforce need support creating a stronger password protocol? EasyLlama’s Cybersecurity & Data Privacy suite of courses can educate employees on the why behind securing your company’s data, and our new Passwords mini-course goes even further in-depth about how to create a strong password. Using interactive knowledge checks and engaging video scenarios, our workplace training is the best solution for keeping your employees up to date on cybersecurity trends and your organizational data secure. Learn more with a free course preview today!