Cyber Threats
In an ever-changing technological landscape, it can sometimes be difficult to notice every new type of cyber attack that's out there. Fortunately, there are many tools and techniques available to help protect your business and ensure you are aware of potential threats.
Impact of Cyber Threats
The impacts of cyber threats can be far reaching, from financial losses to reputational damage to the disruption of critical services. Cyber threats can also undermine trust in an organization’s ability to secure their systems, leading to a lack of public confidence in their security measures. Furthermore, cyber threats can be used for espionage and political manipulation, posing some of the most serious security risks in the digital age.
While some cyber criminals use the telephone to gain illegal access to protected information, email is more commonly used to trick individuals into compromising their security. Some email-based threats include:
Phishing is a form of cyber attack in which a bad actor masquerades as a legitimate entity in order to obtain sensitive information, such as login credentials or financial information, from unsuspecting victims. It typically involves sending fraudulent emails or messages posing as a trusted source, or creating a malicious website that looks like a legitimate one.
Ransomware is a type of malicious software that is designed to block access to a computer system or data until a ransom is paid. It is typically spread via email attachments, malicious downloads, or via exploit kits and can encrypt files on a system or lock the user out of their computer.
Malware is short for malicious software. This is the umbrella term for viruses, worms, trojans, and other harmful computer programs you might have heard of. Bad actors may use such malicious programs to gain access to your data.

How to Protect Against Future Cyber Threats
When it comes to protecting against future cyber threats, it is important to stay informed and up to date on the latest trends in cybersecurity. This includes understanding how cyber threats are evolving and what techniques are being used by malicious actors. Organizations should invest in training their staff on best practices and procedures for responding to cyber threats, as well as regularly assessing their security setup to ensure it meets their organization's needs.
Common Signs of Cyber Threats
Cyber threats are an ever-growing problem in the digital age. They can attack your computer systems and networks, putting your data and sensitive information at risk. It is important to be aware of the common signs of cyber threats so that you can take steps to protect yourself and your organization.
Here are some myths to look out for:
- -
Unusual or suspicious emails
- -
Unfamiliar programs installed on your computer
- -
Pop-up messages with threats or unusual requests
- -
Foreign applications running on your device

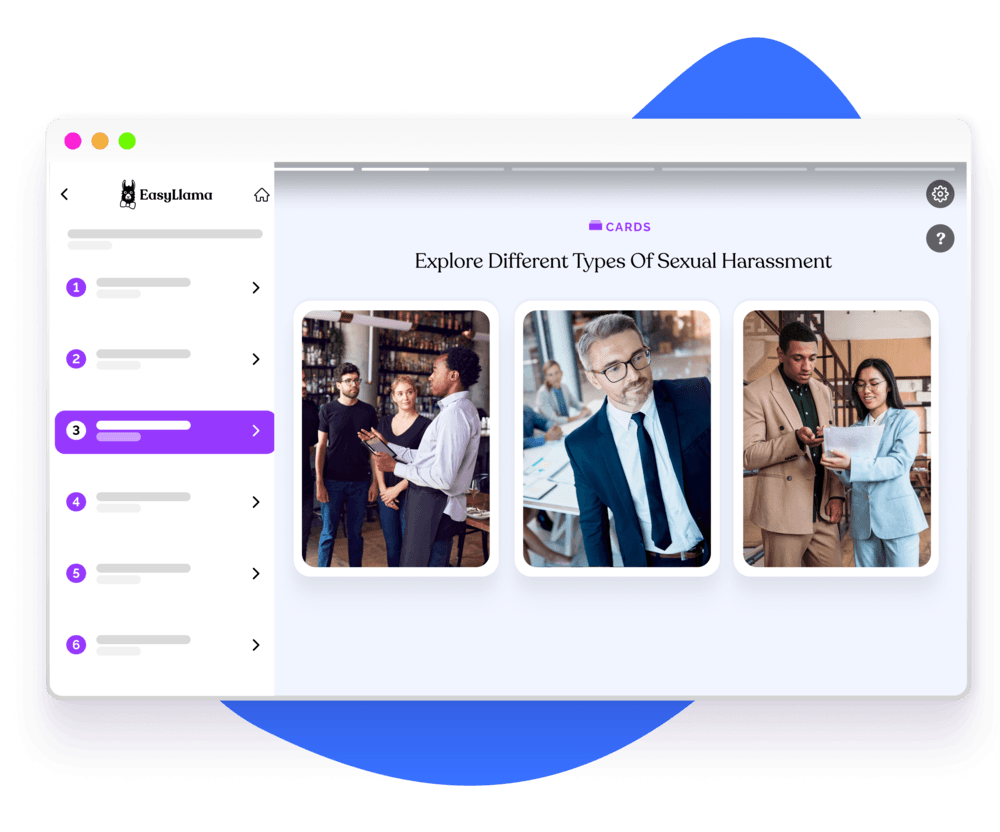
Identify Cyber Threats with Cybersecurity Training
Understanding cyber threats training can provide employees with the knowledge and skills needed to recognize potential threats, ensure that proper procedures are in place to prevent the threats from occurring, and respond appropriately when an attack does occur. Training can also help ensure that employees remain up to date on the latest security protocols and best practices to ensure the safety of the organization's data and systems.
Helping over 8,000 organizations create a safer, more productive workplace
EasyLlama’s online Cybersecurity training course helps prepare employees to navigate the complex world of cybersecurity. With threats increasing and the fines for violations more expensive than ever, implementing a solid cybersecurity plan can help organizations save time and money while avoiding future litigation. The course covers:




Learn more
Cybersecurity Threats FAQs

- Most common types of cyber threats include: - Phishing & social engineering: deceptive emails, texts, or calls that get you to click, share credentials, or pay invoices. - Malware: software designed to damage or spy on systems (e.g., ransomware, trojans, spyware). - Business Email Compromise (BEC): impersonating executives or vendors to reroute payments. - Password attacks: credential stuffing, brute force, or guessing weak/reused passwords. - Insider threats: mistakes (misdirected emails, wrong sharing settings) or malicious actions. - Vulnerability exploits: attackers abusing unpatched software or misconfigured cloud services. - DDoS: flooding a service with traffic to knock it offline. - Supply-chain attacks: compromising a trusted vendor or software update to reach many targets at once. - IoT & mobile risks: insecure devices, apps, and endpoints outside the office perimeter.
- The most common sources of cyber threats are: - Cybercriminals seeking money (ransomware, BEC, data theft for resale). - Nation-state or advanced groups targeting IP, critical infrastructure, or sensitive data. - Insiders—both negligent (accidental data exposure) and malicious (theft, sabotage). - Third-party vendors/partners with network access or who handle your data. - Automated bots scanning the internet for known weaknesses within minutes of disclosure.
- The best defense against common cyber threats is layered and requires people, process, and technology working together. Start with people—provide ongoing security awareness training so employees can spot phishing and handle data safely. Require strong authentication (MFA) and a password manager to eliminate reuse, and keep policies simple and clear so everyone knows how to handle data and report incidents. On the process side, keep systems patched on a schedule and fast-track critical fixes. Limit access with a least-privilege approach and review permissions regularly. Maintain tested backups (3-2-1 rule) and a straightforward incident response plan that outlines roles and steps. Don’t forget vendor diligence—perform basic security checks on partners that touch your data. For technology, layer tools that reduce risk without creating friction: email and web filtering, EDR/antivirus, and full-disk encryption on devices. Lock down cloud and mobile configurations with automatic updates and MDM, centralize logs in a SIEM for alerting, and segment your network with firewalls and DNS filtering to contain threats.
- Cyber threats have shifted from broad, noisy attacks to targeted, business-savvy campaigns. Early mass spam and simple malware gave way to spear-phishing and business email compromise that exploit trust and context. Ransomware evolved from basic file-locking to “double/triple extortion,” where attackers also steal data and threaten leaks. As work moved to cloud and SaaS, identity and configuration weaknesses became prime targets, while supply-chain compromises let attackers reach many organizations at once. Remote and mobile work expanded the attack surface across home networks, IoT, and OT devices. Today, automation and AI accelerate everything—more convincing lures, faster exploit development, and near-instant scanning for newly disclosed flaws—so speed, visibility, and resilient processes matter more than ever.
















