Phishing Red Flags: Recognizing and Avoiding Online Scams


The convenience of the internet comes with a number of potential dangers, and one of the most prevalent online threats is phishing scams. These malicious attempts to steal sensitive information are ever-present, and it's crucial for every employee to be vigilant and aware of the red flags associated with them. In this article, we'll explore the world of phishing, identify phishing red flags, and discuss how to protect yourself from falling victim to online scams.
What is Phishing? Understanding the Threat
Let's start with the basics. Phishing is a form of cyber crime where scammers impersonate legitimate organizations or individuals to trick people into revealing sensitive information such as passwords, credit card numbers, or social security numbers. These criminals have a variety of malicious goals, but their top priority is to exploit your trust and access your valuable data.
Generic Salutations and Urgent Requests
Phishing emails often begin with generic greetings like "Dear Customer" or "Hello User." Legitimate organizations usually address you by your name. Additionally, they may try to pressure you into immediate action by creating a sense of urgency, claiming that your account will be suspended or you'll face legal consequences if you don't act immediately. Recognize these tactics as warning signs of a potential phishing attempt.
Suspicious Links and URLs
Emails that are meant to attract phishing victims are often embedded with links that direct you to fake websites designed to mimic trusted ones. Before clicking on any link, hover your mouse over it to reveal the true destination in the status bar. If the URL doesn't match the legitimate website's domain, it's likely a phishing attempt.
Be Cautious with Shortened URLs
Shortened URLs, commonly used in phishing emails, can obscure the true destination, making it difficult to discern whether a link is safe or not. To ensure your online safety, consider using URL expanders or contacting the sender directly to confirm the link's authenticity before clicking. Taking these precautions can prevent you from falling into a phishing trap.
Unusual Sender Addresses
Phishers often employ deceptive tactics when crafting sender addresses. They may use fake addresses that closely resemble legitimate ones, such as "yourbank@gmail.com" instead of the genuine bank's domain. It's essential to scrutinize sender addresses for any inconsistencies or misspellings to detect potential phishing attempts.
Requests for Personal or Financial Information
Receiving an email that requests personal or financial information should immediately raise a red flag. Legitimate organizations, especially banks and government agencies, rarely, if ever, ask you to share sensitive information via email. Be cautious and prioritize verifying the email's authenticity through official channels before divulging any confidential data.
Poor Grammar and Spelling
Some phishing emails contain glaring errors in grammar and spelling. Legitimate organizations invest in proofreading their communications, so encountering frequent mistakes in an email should raise skepticism. In other cases, phishers will include typos in order to fake an email from a friend or coworker, using the errors to look more like a real person. Take the time to closely examine the email's content for linguistic errors as a strong indicator of a potential phishing scam.
Unexpected Attachments or Downloads
Cyber criminals often use attachments in phishing emails to conceal malware or viruses designed to compromise your device or steal your data. To stay safe, never open an attachment or download a file from an unknown source. Always verify the sender's identity and the content's legitimacy before taking any action, as clicking on a malicious attachment can have severe consequences.
Verify Identity and Sources
When you find yourself in doubt about an email's authenticity, it's wise to take steps to verify its legitimacy. Reach out to the organization directly using official contact information obtained from their official website or previous correspondence. Avoid relying on contact details provided within the suspicious email itself, as phishers often manipulate these to deceive recipients.
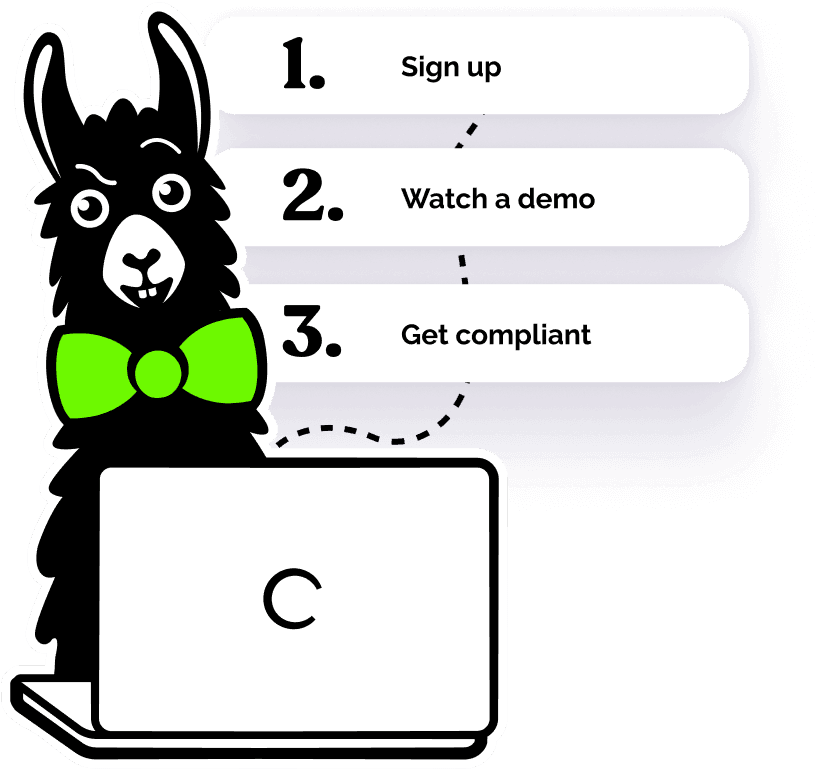
By staying informed and aware of these phishing red flags, you can significantly reduce the risk of falling victim to phishing scams. One of the best ways for employers to keep their organizations safe from phishing attempts is with Cybersecurity training. EasyLlama’s online courses, including our mini-course all about Phishing, can educate your employees about how to prevent phishing and why cybersecurity is so important. Using interactive quizzes and real-life video scenarios, EasyLlama’s 100% mobile-friendly training helps employees both learn and retain important data privacy knowledge to keep your organization safe. Learn more with a free course preview today!